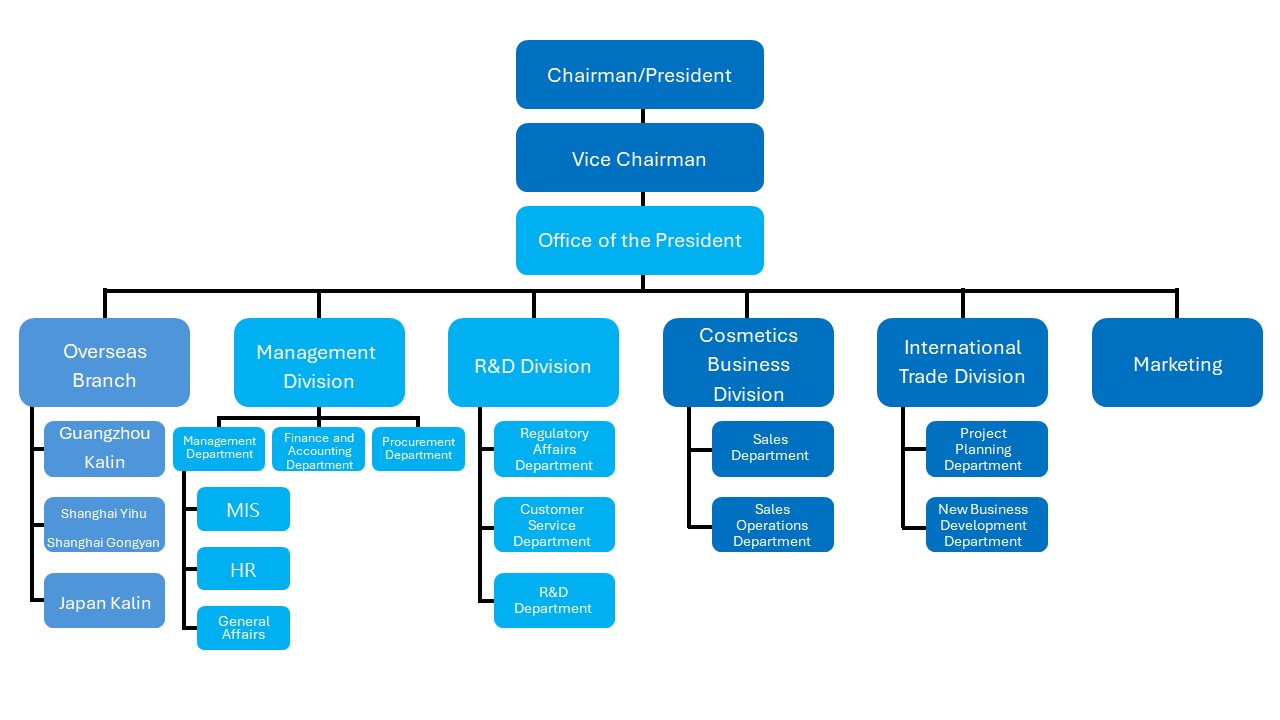
|Organizational Structure|
|Management Team|
|
Position |
Name |
Date of Appointment |
Current Main Duties |
|
董事長 |
林震宙 |
2000.09.18 |
香林企業(股)公司董事長兼總經理 香霖國際貿易(廣州)有限公司董事長 |
|
副董事長 |
吳少君 |
2000.09.18 |
香林企(股)公司副董事長 香林企(股)公司管理處主管 |
|
研發處協理 |
陳金鳳 |
2001.07.01 |
香林企業(股)公司研發處協理 |
|
化妝品事業處經理 |
蔡俊泓 |
2003.09.15 |
香林企業(股)公司化妝品事業處經理 |
|
副總經理 |
陳志銘 |
2001.02.02 |
香霖國際貿易(廣州)有限公司副總經理 |
|
副總經理 |
林彥同 |
2016.04.07 |
怡滬國際貿易(上海)有限公司副總經理 上海工妍國際貿易有限公司副總經理 |
|
社長 |
林彥廷 |
2019.08.01 |
Nipponkoulin Enterprise Co., Ltd. 社長 |
|Audits|
Our company obtained the ISO 9001:2015 certification in 2015. In addition to the regular annual external audits, we arrange relevant courses for internal audit personnel and ensure the regular execution of internal audits. The internal audit procedure is clearly defined to review the company's operational procedures and internal controls, and report whether the design of such controls is suitable for routine operations, as well as their effectiveness and efficiency. The scope covers all company operations.
Audit work can also be conducted as project audits or reviews based on needs, providing timely reports to management to help them understand existing or potential issues by examining general audit results and project execution status.
Internal audits review the self-checks conducted by each department, including checking whether the tasks are executed and reviewing documents to ensure quality in execution. The comprehensive results of self-checks are then reported to the Chairman.
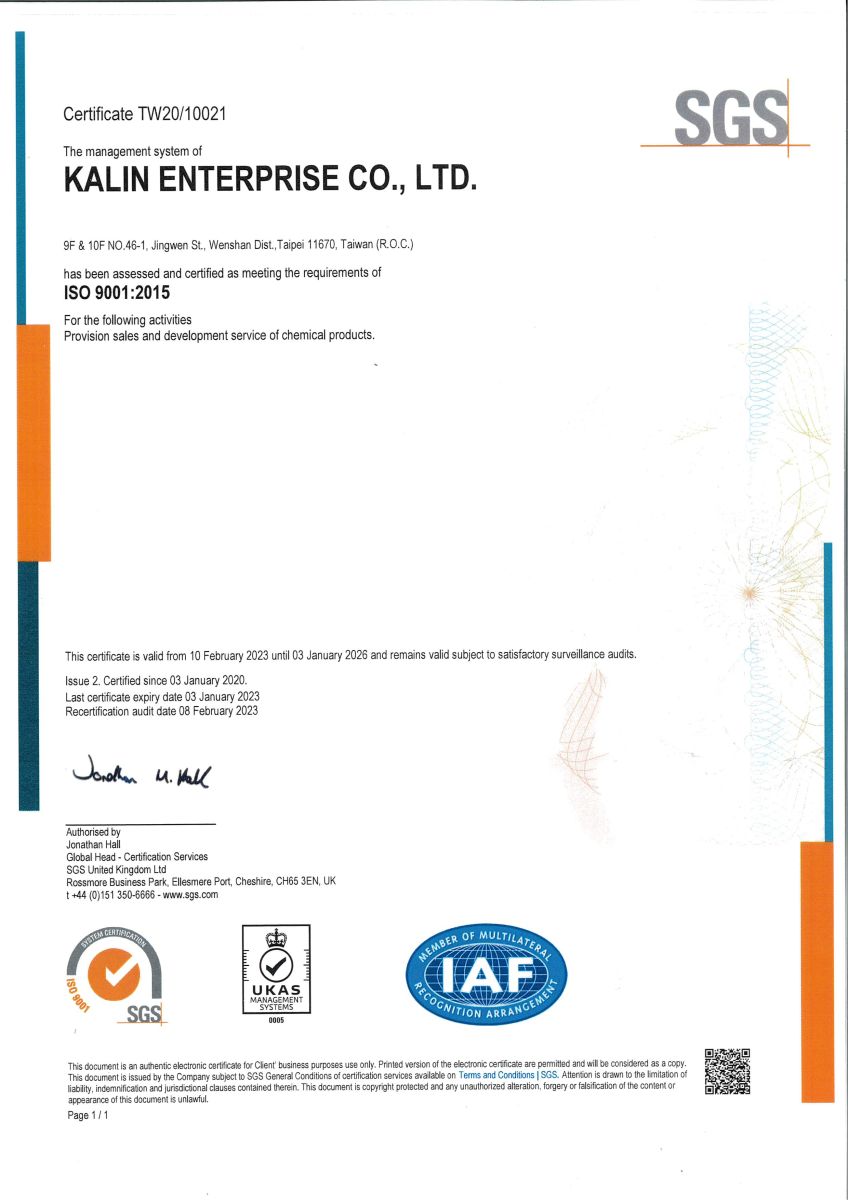
ISO 9001:2015 Certificate Download
|Information Security Management|
▶︎ Information Security Roles and Responsibilities
Information personnel assist departments in conducting risk assessments, security classification, and implementing system security control measures. If departmental data is made accessible to external departments for data retrieval, appropriate restrictions and security control procedures must be established to prevent unauthorized access to information.
▶︎ Personnel Security Management and Education/Training
Employees whose duties involve handling sensitive IT resources or confidential information must undergo appropriate security evaluation procedures. Employees are required to maintain confidentiality as per relevant regulations and participate in proper information security education and training.
Information personnel are prohibited from granting system access services to users before they complete formal authorization procedures. Users must be fully informed about the terms and conditions of system access and are only allowed to access system resources within their authorization.
Users must not share their personal login credentials (username and password) with others, nor should they attempt to acquire others’ credentials by any means.
System user registration records must be created and maintained for future reference. When users are transferred, resign, or take leave, their system access permissions must be promptly revoked. If there are signs that a user's password may have been compromised, it must be immediately changed.
▶︎ Computer System Security Management
Establish and regularly update an inventory of information assets.
Manage the security of equipment and peripherals.
Implement network security management.
Enforce system access controls.
▶︎ Security Management for System Development and Maintenance
Application software executed on operating systems must strictly follow control procedures to minimize risks that may affect the operating system.
1.1. If operating system changes are necessary, an evaluation must be conducted to assess whether the changes negatively impact application systems or introduce security risks.
1.2. Any operating system changes must be promptly communicated to relevant personnel to ensure sufficient evaluation is conducted before the changes are implemented.
Anti-virus programs must be scheduled for regular updates and comprehensive scans of computer equipment.